 Although, we do not recommend setting a simple password as your Windows password, you can make it harder for users to get access even if you have a simple one: Block them after X failed logins. Handy!
Although, we do not recommend setting a simple password as your Windows password, you can make it harder for users to get access even if you have a simple one: Block them after X failed logins. Handy!
Let’s say you are sharing your PC with other people, then you may not want them to access your account. If you have administrator access, you can use the security policy editor to lock out users that enter wrong passwords. This will be mostly useful to system administrators, but maybe someone of you wants to use it as well. Here’s how.
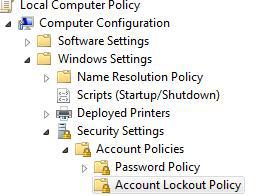
1. Step Enter gpedit.msc into the search bar and hit enter
2. Step Uncollapse Computer Configuration, Windows Settings, Security Settings, Account Policies, Account Lockout Policy as seen below:
3. Step Now, in the right pane simply double-click Account lockout threshold and set the value to X failed logins. If you want to block users after 1 login then enter 1, 2 then 2 and so on. I recommend to set this to 4 or so – if you forget your password you have at least a couple tries to get it right before being locked out for X minutes
Click Apply
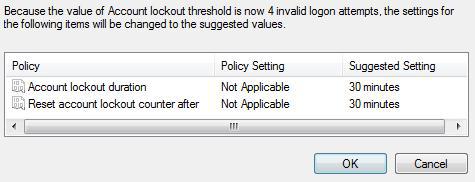
4. Step Windows will now suggest some settings:
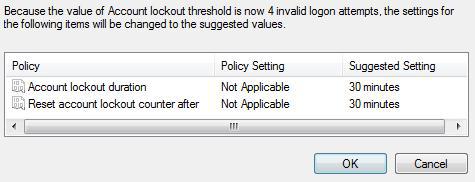
It will sett the lockout duration to 30 minutes and the reset account lockout counter to after 30 minutes
4. Step If you are not happy with the suggested values, double-click on Account lockout duration and specify a number for the length of the lockout. Do not set this too high
That’s it, you can block user accounts that enter a wrong password. Great for admins or shared PC’s