Are you in full control of your computer? Do you really know what process is running in the background and what tool on your PC requires a connection to a server in russia?

If you want to take over control, you will need a good process manager for Windows 7. Oh, I don’t say that built-in process manager is bad, but if you compare it with 3rd-party tools, you will finally find out what real control is.
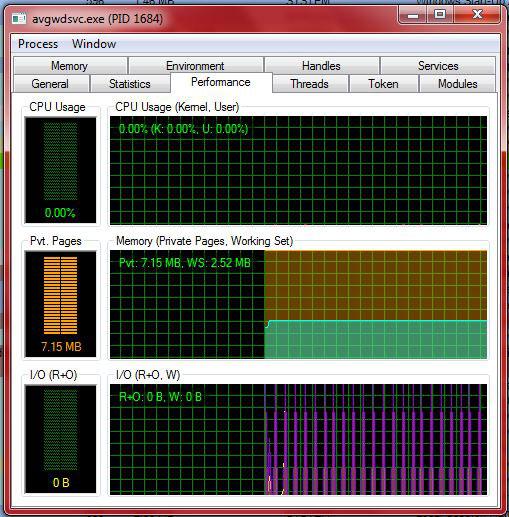
Process Performance
Ever wondered how firefox is doing recently or how your game performs on your PC?
ProcessHacker for Windows 7 allows you to keep track of the performance of all services and processes running on your PC:
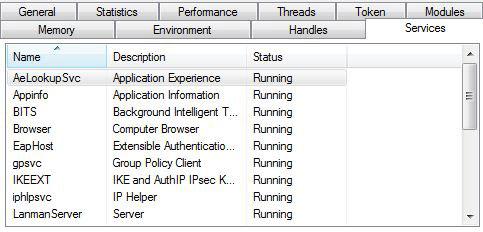
Which service is running that process?
Not even the pros know all services, but they know where to look to find it out. A process manager can help you to identify services and processes. It is important that you know what services are currently running on your PC. If you don’t, you might as well turn of your firewall or your Anti-Virus.
1. Step Open Process Hacker
2. Step Right-click on an .exe file and click on “Properties”
3. Step If the exe file is running a registered service on your PC, you will find it under the tab “Services”
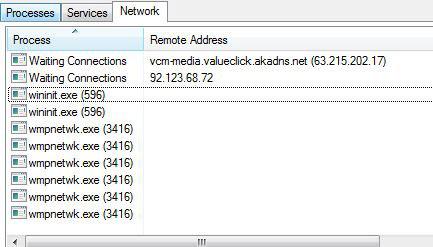
My PC has a connection to IP xx.xx.xx.xx, what is it?
Sometimes we are all a little bit paranoid, especially when it comes to internet security. It is good to know what process is establishing your connections. I guess some people can sleep better at night knowing what process hacker abuse to attack them ;)
Seriously, if you want to track down your connections, ProcessHacker comes with another awesome feature:
Find Rootkits + hidden processes
A hacker can use rootkits to replace system exe files, which may then be used to hide processes and files the attacker has installed, as well as the rootkit itself.
Process Hacker can also detect hidden processes of rootkits.
Download Process Manager
You can download Process Hacker from Sourceforge:
System Requirements:
- .NET Framework 2.0
- Microsoft Windows XP SP2 or above, 32-bit or 64-bit. Please note that certain functionality including detection of hidden processes, full control over all processes and the ability to protect/unprotect processes is only available on 32-bit systems.